The modern digital landscape requires organizations to establish dedicated server security because it has become essential for business operations. Dedicated servers function as essential components for organizations which need to manage their mission-critical operations and handle high-volume online activities and protect their confidential information. But this depth of control also comes with an equal level of responsibility. Without the right security framework in place, a powerful server can become an easy target. A practical Dedicated Server Security Framework should focus on three pillars: Firewalls – DDoS Protection – Access Control. The truth is that dedicated servers are attractive targets.
Why Dedicated Server Security Matters More Than Ever
Dedicated servers become appealing targets because their owners possess extensive operational privileges while their systems contain important confidential information. Attackers can use one security flaw to enter the system and steal customer data and create service interruptions through web request malware attacks or they can take control of your entire network system.
Key risks include:
- Weak credentials resulting in unauthorized access
- Misconfigured services exposed to the public internet
- Large scale DDoS attacks that exhaust server resources
- Insider threats due to bad access management
Insider threats caused by poor access management; poor internal security practices can destroy.
Firewall Protection: The First Line of Defense
The firewall creates a protective barrier which separates your server from internet access. Your server firewall will only allow legitimate traffic to access your system.
Types of Firewalls for Dedicated Servers
- Network Firewalls
Network Level Firewalls process every network packet by checking its source IP address and destination IP address and port numbers and protocol types. - Host-Based Firewalls
Setup on the server itself (iptables or firewalld) – ability to control inbound and outbound traffic fairly completely. - Hardware Firewalls
Provided by hosting providers, another filtering layer is added before the traffic reaches the server.
Dedicated Server Firewall Rules: Best Practices
The dedicated server firewall rules require proper design when they need to achieve two main goals:
- The system needs to allow only specific ports which include 80 and 443 and 22.
- The system needs to permit SSH access from designated IP addresses only.
- Block unused services entirely.
- Log and monitor any denied connection attempts.
The main cause of server breaches occurs because security settings of firewalls fail to work properly and regular audits verify that firewall security policies meet application requirements.
DDoS Protection for Dedicated Servers
DDoS protection services safeguard dedicated servers from Distributed Denial-of-Service attacks which target servers by overwhelming them with excessive traffic until they stop functioning. Organizations require DDoS protection services for dedicated servers because attackers can destroy their trustworthiness and financial stability within two minutes.
How DDoS Attacks target Dedicated Servers
With shared hosting the load of an attack will be spread between multiple users. With a dedicated server the full force of an malicious attack is absorbed by one machine, unless mitigation is applied CPU, Memory and Bandwidth will all be exhausted in minutes.
Common types of attacks include:
- Volumetric Attacks – saturate the bandwidth
- Protocol attacks – these are attacks that exploit server resources (processing capacity or bandwidth) so that the server can no longer service legitimate requests.
- Application-layer attacks – these are attacks that target specific services or functions of a server application or service.
Application-layer ddos attacks are able to more effectively and accurately use up and exceed the resource limits of applications or services running on a targeted server.
Effective DDoS Mitigation Strategies
Dedicated server security requires implementation of multiple DDoS protection methods through a comprehensive security system:
- Traffic filtering and rate limiting
- Automated detection systems
- Scrubbing centers that remove malicious traffic.
- Upstream protection from the hosting provider
Server-level defenses combined with provider-level mitigation provide the best overall protection against large-scale attacks.
Access Control: Preventing Unauthorized Entry
External threats may be scary, but most breaches start with weak internal security. Dedicated server access control makes sure that only allowed users are able to interact with sensitive systems.
Key Access Control Mechanisms
- Least Privilege
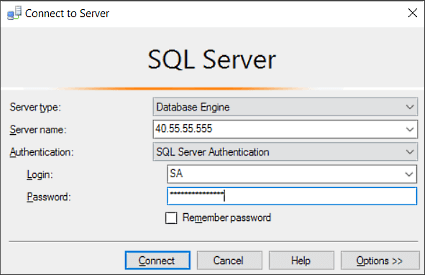
All Users should have the least access necessary to get their job done, and no more. - Secure Authentication Methods
- ssh uses ssh key-pairs to authenticate ssh logins
- Multi-factor authentication (MFA)
- Strong password policies
- Role Based Access Control (RBAC)
Utilize RBAC to specify and manage access rights for users.
Monitoring and Audit Trails
Assign permissions to job functions rather than individual user accounts in order to minimize error. Monitor, log and review the access events as well as user activities throughout the lifecycle of the system use for detecting early warning signs of abuse or to meet regulatory conditions.
Network Security for Dedicated Servers
Not only access control and firewalls, but the network security as a whole for your dedicated servers guarantees a safe communication between all services.
The four essential protocols for encrypting data during transmission include:
- Encrypted data transmission (TLS/SSL)
- Secure DNS configurations
- IDS/IPS= intrusion detection and prevention system
- Segmentation of internal services
A hardened network environment reduces lateral movement in the event an adversary gains a foothold.
Server Security Best Practices You Should Not Ignore
A reliable dedicated server security framework is not a one time configuration, it also requires ongoing maintenance and vigilance.
Essential Practices
- Regular OS and software updates
- Automated security patching
- Malware and rootkit scanning
- Encrypted backups stored offsite
- Continuous monitoring and alerting
Security systems depend on The security process requires ongoing monitoring because it needs continuous system surveillance.
Secure Dedicated Server Hosting: Provider’s Role
Server security, even with perfect configuration, depends on hosting environment to some extent. And secure dedicated server hosting provides several in-built protections like:
- Physical data center security
- Network level firewalls
- Redundant infrastructure
- 24/7 monitoring and response teams
A good hosting provider will have a layered approach to security, not simply providing security in lieu of your own efforts.
Building a Complete Dedicated Server Security Framework
When used in combination, firewalls, DDoS protection and access control form a powerful adaptive defense mechanism. With this layered defense, if one of the defensive measures fails or is performed poorly the others continue to protect the server.
Well developed security for dedicated servers:
- Minimizes the risk of downtime
- Reduces the risk of a data breach
- Improves compliance readiness
- Builds trust with customers over the long term
Conclusion: Security Is a Strategic Investment
The dedicated server enables users to access powerful computing and flexible system operation but this performance capacity requires protection through appropriate security measures. You have to put in place very good firewalls because what were talking about is very serious security threats, and you have to add strong DDoS defense for dedicated servers and more traditional access control,” said Petkov. In the huge risky world of internet digital…With great proactive server security best practices, businesses can remain robust, and competitive alongside being compliant too!
This article is described by a server infrastructure and security specialist with 10+ years experience in design, operation and management of secure hosting environments including network security for dedicated servers, firewall architecture and enterprise-grade DDoS mitigation. He has helped many e-commerce, SaaS and finance businesses to design cost effective yet scalable and highly secure server frameworks with guaranteed uptime and compliance.